Addiction treatment works best when you feel safe sharing your story. At EveningIOP, we know that privacy concerns often keep people from seeking help they desperately need.
Fear of exposure, job loss, or judgment shouldn’t stand between you and recovery. This guide shows you how privacy-focused addiction treatment protects your confidentiality at every step.
Why Privacy Really Stops People From Getting Help
Stigma around addiction treatment isn’t theoretical. It’s the reason someone stays silent when they need help most. A person worried about their employer finding out they’re in treatment, or a parent afraid their children will be taken away if records surface, will delay seeking care indefinitely. This isn’t about hurt feelings. It’s about real consequences. HIPAA protects addiction treatment information separately from other medical records under 42 CFR Part 2, but most people don’t know this protection exists. They assume any mention of treatment will follow them everywhere. That fear alone keeps millions from getting treatment. The confidentiality protections under Part 2 help address concerns that discrimination and fear of prosecution deter people from entering treatment.
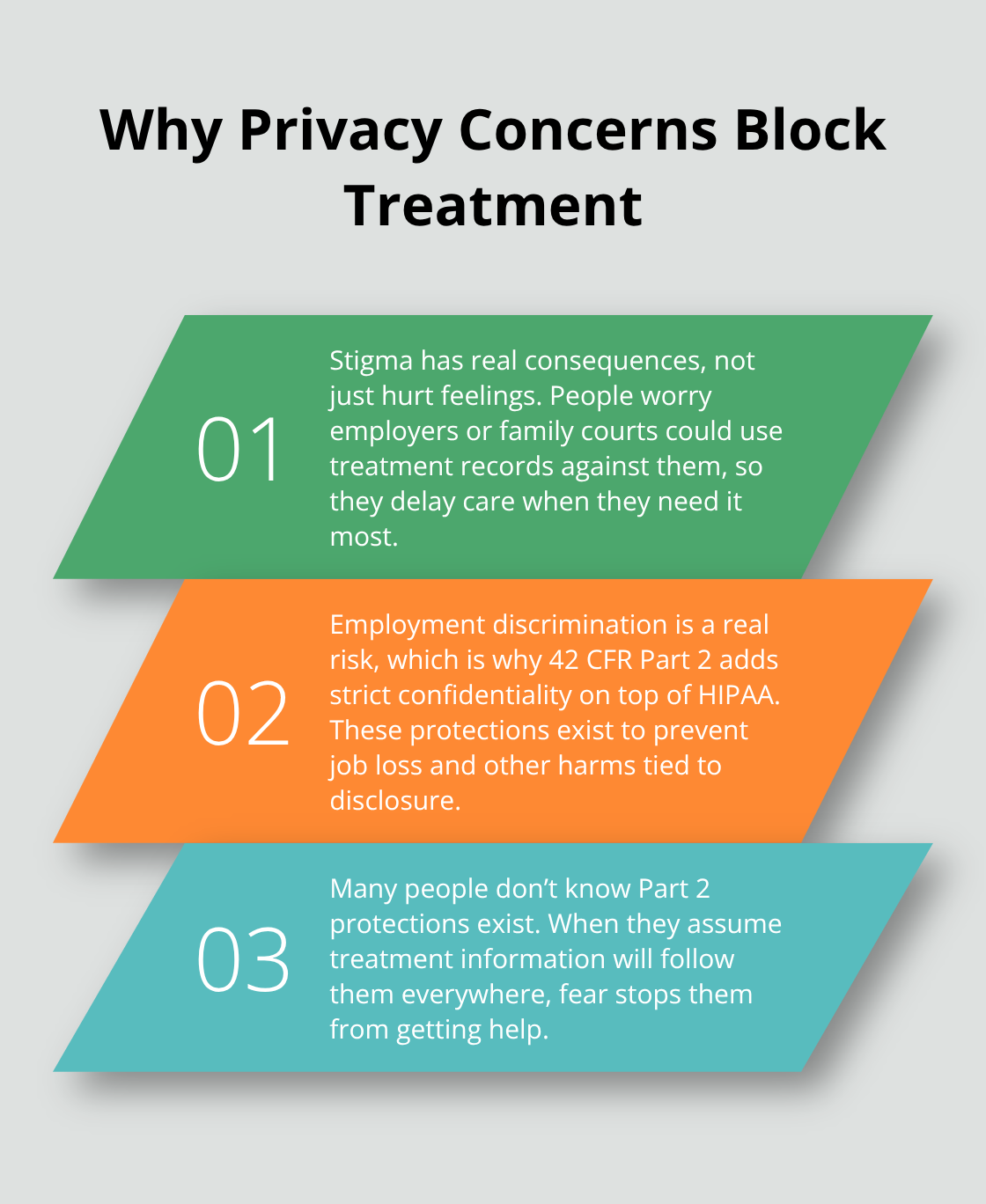
Yet if you don’t know these protections exist, they don’t help you at all.
Job Loss Is a Real Threat People Face
Employment discrimination happens. Someone in recovery attends a treatment program and later gets passed over for promotion because a coworker found out. A person loses their job after a supervisor learns about their treatment. These aren’t edge cases. The legal system recognizes this risk so clearly that confidentiality protections exist precisely to prevent it. Under Part 2, your treatment status cannot be disclosed to your employer without your explicit written consent. Insurance companies also cannot use addiction treatment information to deny coverage or raise rates in most situations, though the rules around insurance vary by state. What matters is understanding your specific rights before entering treatment. Ask your treatment provider directly: Can my employer access my treatment records? What about my insurance company? How long do you keep my data? A provider who can’t answer these questions clearly is a red flag. One who explains your specific protections upfront is one you can trust.
Disclosure Happens When You Don’t Expect It
Telehealth data breaches have exposed thousands of addiction and mental health records. In 2023, 725 data breaches were reported to OCR and across those breaches, more than 133 million records were exposed or impermissibly disclosed. These weren’t small mistakes. They were systemic failures in how patient data was handled. Addiction treatment records sell for up to 1,000 dollars each on the dark web, creating strong financial incentives for data theft. This means your provider’s security practices matter enormously. Encryption, access controls, staff training, and regular security audits separate trustworthy providers from risky ones. Ask whether your potential treatment provider uses encryption for all sensitive files, restricts access to authorized staff only, requires multi-factor authentication, and conducts regular security audits. These aren’t optional features. They’re essential.
What Separates Safe Providers From Risky Ones
Your treatment provider’s approach to data security reveals whether they truly prioritize your confidentiality. Trustworthy providers encrypt all sensitive files and communications to protect your information both at rest and in transit. They restrict access to your records to authorized individuals on a strict need-to-know basis. They train all staff on data-security best practices to reduce phishing, social engineering, and insider threats. They implement data retention limits by assigning sensitive records a defined lifespan and secure deletion timelines. They conduct regular security audits and vulnerability assessments to identify and fix weaknesses before breaches occur. They require multi-factor authentication for access to sensitive systems and data. They avoid tracking tools that relay patient information to third parties for advertising purposes. They verify that third-party service providers comply with applicable data-privacy and security regulations through contractual requirements and due diligence. When you evaluate a treatment program, these practices should form the foundation of your decision. A provider who can explain their security infrastructure in plain language and answer your questions without hesitation has earned your confidence. One who deflects or offers vague answers about how they protect your data signals that privacy isn’t truly their priority.
How Providers Actually Protect Your Data
HIPAA compliance means your addiction treatment records stay separate from your general medical file, but separation alone doesn’t stop breaches. Real protection requires multiple layers working together. Encryption protects data at rest and in transit, making it unreadable to anyone without the decryption key. Access controls limit who can view your records to staff members who genuinely need them for your care. Multi-factor authentication adds a second verification step so someone cannot access your data with just a stolen password. Regular security audits identify vulnerabilities before hackers exploit them.
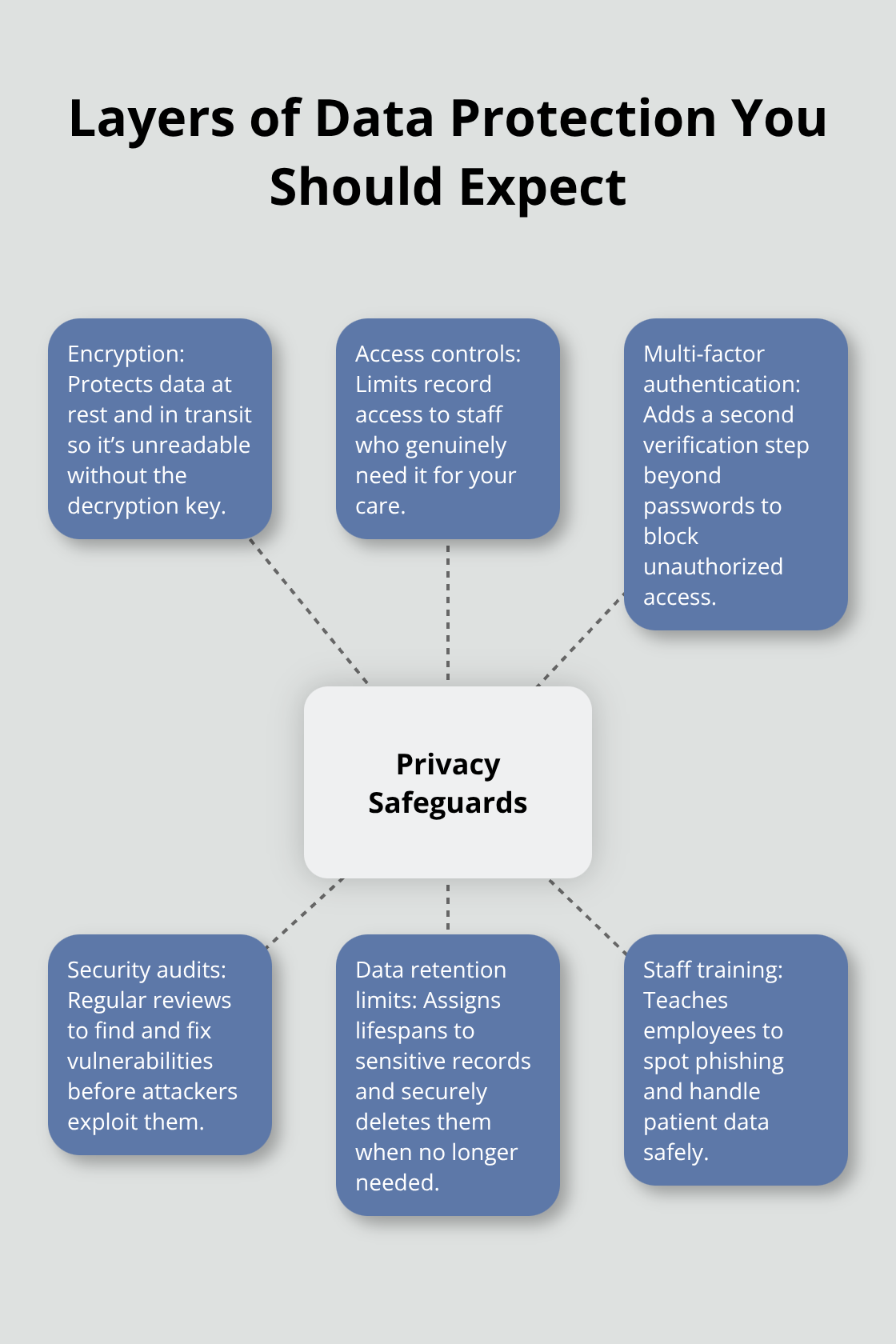
These practices aren’t optional. They’re the difference between a provider who talks about privacy and one who actually implements it.
Encryption and Access Controls Form Your First Line of Defense
Ask potential providers whether they encrypt all sensitive files, restrict database access to authorized personnel only, and require multiple authentication factors for staff logins. If they cannot explain their specific security measures in plain language, that’s a warning sign. Trustworthy providers discuss their infrastructure openly because they have nothing to hide. Encryption protects data at rest and in transit, making it unreadable to anyone without the decryption key. Access controls ensure that only clinicians and billing staff who work directly with your care can view your records. Multi-factor authentication prevents unauthorized access even if someone steals a password.
Telehealth Platforms Demand Extra Security Vigilance
Telehealth platforms introduce specific risks because data travels across the internet, making encryption especially critical. When Confidant Health left 5.3 terabytes of patient data unprotected in a publicly accessible database, it exposed psychosocial assessments, audio recordings, and insurance information. That breach happened because the company failed to implement basic security controls, not because telehealth itself is inherently unsafe. The Department of Health and Human Services recommends that providers implement data retention limits, assign defined lifespans to sensitive records, and delete them securely when no longer needed.
Staff Training and Third-Party Accountability Matter Enormously
Staff training matters enormously because employees often represent the weakest link in security. Phishing emails that trick staff into revealing passwords cause real breaches. Providers should train all staff on recognizing social engineering attempts and handling patient data safely. Confidentiality agreements establish legal accountability when staff members violate privacy. Third-party service providers like billing companies or cloud storage vendors need contractual requirements ensuring they comply with HIPAA and Part 2 regulations.
Evaluate Provider Security Before You Commit
Before selecting a treatment program, ask whether they conduct regular security audits, provide staff training documentation, and verify third-party compliance through written contracts. A provider who answers these questions confidently and specifically has built privacy into their operations from the ground up. These same security standards also determine how providers handle the red flags you should watch for when evaluating your options.
Red Flags That Signal Privacy Isn’t a Priority
When a treatment provider cannot articulate their privacy practices in plain language, that silence speaks volumes. Providers serious about confidentiality explain how they protect your data without requiring you to ask follow-up questions or decode technical jargon. If you contact a program and staff cannot tell you whether they encrypt all sensitive files, how they restrict access to your records, or what happens to your data after treatment ends, move on. This isn’t about being overly cautious. The Federal Trade Commission fined BetterHelp $7.8 million for sharing sensitive mental health information with third parties for advertising, and Cerebral faced a $7 million penalty for misrepresenting privacy practices. These companies operated nationally and claimed to prioritize patient privacy. Yet their actual practices contradicted their promises. The difference between a trustworthy provider and a risky one often comes down to whether they answer your specific questions directly or deflect with vague assurances.
Outdated Technology Signals Weak Security
Outdated technology represents another critical warning sign. If a treatment program still uses paper records, fax machines for sensitive communications, or software that hasn’t been updated in years, their infrastructure cannot meet current security standards. Ask whether your provider uses cloud-based systems with encryption, whether they conduct regular security audits, and whether they require multi-factor authentication for staff accessing patient data. A provider using outdated platforms may claim they prioritize privacy, but outdated systems cannot implement modern encryption or access controls. The absence of modern technology directly correlates with higher breach risk.
Vague Data Sharing Policies Hide Real Problems
The absence of clear written policies about data sharing represents a major red flag. Your treatment provider should have a privacy policy you can read before you start treatment, not one they hand you during intake with no time to review. That policy should specify exactly which third parties can access your information, under what circumstances they can access it, and what happens if you want to restrict sharing. When providers are vague about data sharing or claim their policies are confidential, they signal that privacy protection isn’t genuinely built into their operations. Transparent providers make their data-sharing practices immediately available and answer your questions without hesitation.
Direct Questions Reveal True Priorities
Contact potential providers and ask specific questions about their security practices. Request information about their encryption methods and access control procedures and data retention timelines. Ask whether they conduct regular security audits and how they verify that third-party vendors comply with privacy regulations.
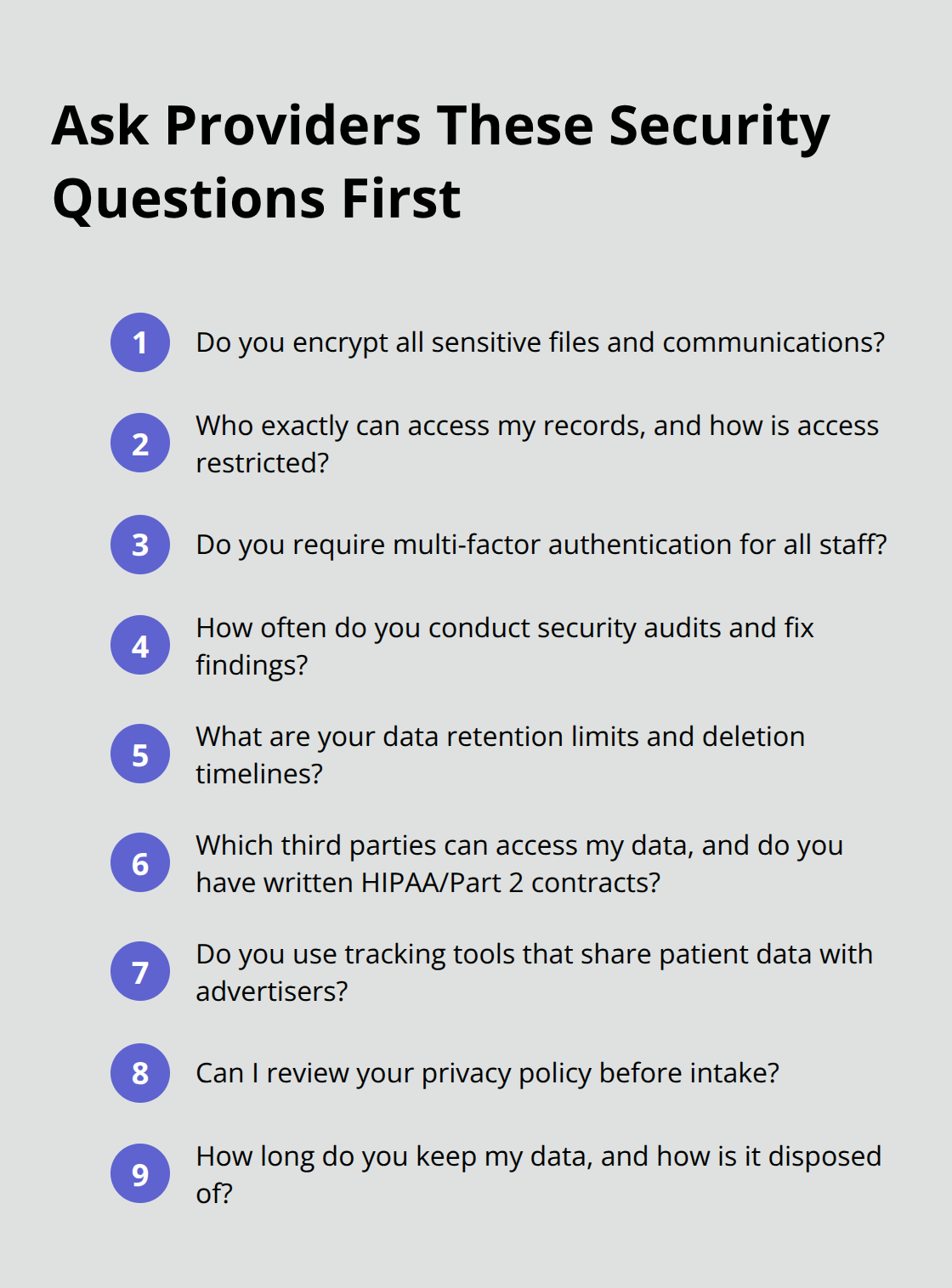
Providers who answer these questions directly and provide documentation have built privacy into their operations from the ground up. Those who deflect, offer vague responses, or claim they cannot discuss security details reveal that privacy isn’t truly their priority.
Final Thoughts
Privacy-focused addiction treatment protects you at your most vulnerable moment, allowing you to focus entirely on recovery without fear of exposure or judgment. Contact programs and ask whether they encrypt all sensitive files, restrict access to authorized staff only, conduct regular security audits, and verify that third-party vendors comply with privacy regulations. Providers who answer these questions clearly and provide documentation have built privacy into their operations from the start, while those who deflect reveal that confidentiality isn’t truly their priority.
Your treatment journey belongs to you, and you control what information gets shared and with whom. Before committing to any program, review their written privacy policy, understand your rights under HIPAA and 42 CFR Part 2, and confirm that they use modern encryption and access controls. Ask about their data retention practices and what happens to your records after treatment ends.
We at EveningIOP understand that privacy concerns often keep people from seeking help, which is why we prioritize security in every aspect of our evening IOP programs. Your recovery deserves a provider who treats your privacy as seriously as your treatment.


